What’s up, everyone!
I know! I can already hear you thinking: “What’s that? Cloud PCs in your Active Directory?” Yes, that’s possible! Until now I always used Microsoft Entra joined Cloud PCs together with Intune to manage Cloud PCs. But what happens when you are in a situation where you need to use hybrid Microsoft Entra join? Well, look not further! I got you covered!
Microsoft Entra join vs Hybrid Microsoft Entra join
It might be a good idea to start this post with a short comparison between the two.
Microsoft Entra join
These devices are joined to Microsoft Entra only and they are arguably the easiest to manage using Microsoft Intune.
Hybrid Microsoft Entra join
These devices are joined to Active Directory (AD DS) and then synchronized to Microsoft Entra. Management of these devices can be done via Group Policies (GPO) and/or Microsoft Intune. Be aware that you need to configure a couple of things before hybrid Microsoft Entra join works:
- A line of sight to the domain controllers.
- Microsoft Entra Connect .
- Cloud PCs deployed using Hybrid Entra Join can only be assigned to hybrid users. Cloud only users cannot use hybrid Cloud PCs.
Prerequisites for an Azure network connection
The following are prerequisites for an Azure network connection:
- An account that is a member of one of the following roles: Intune administrator, Windows 365 administrator or Global administrator.
- The Subscription reader role on the subscription that contains the VNET.
Step 1: Configure the Azure network connection
All of the configuration of the Azure network connection is done via the Microsoft Intune admin center, assuming that the networking and domain controllers are prepared.
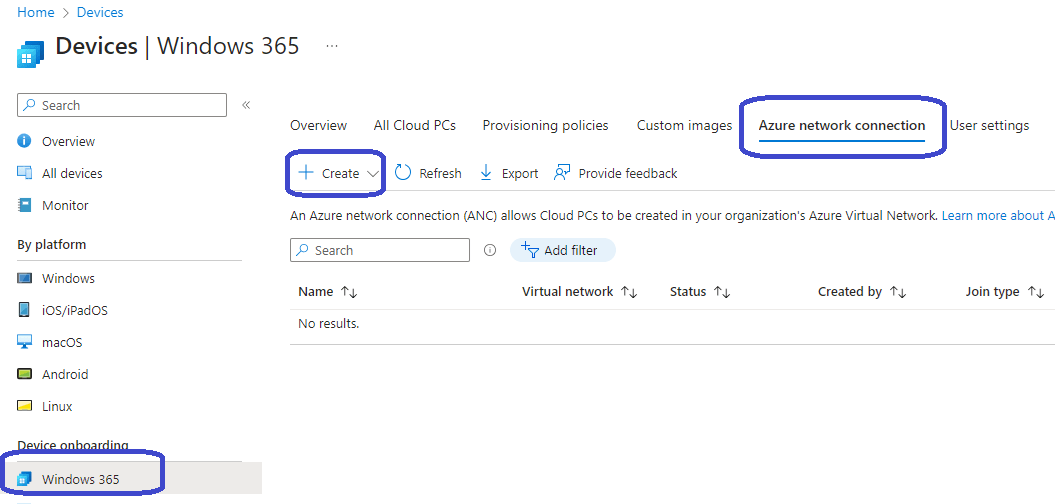
Go to Devices, Windows 365, Azure Network connection. Click on the + Create button in the ribbon.
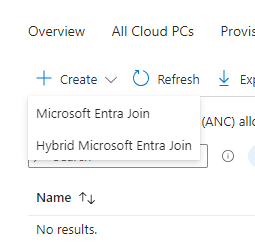
There are two choices here:
- Microsoft Entra Join: select this option if you want to use your custom VNET while joining the Cloud PC to Microsoft Entra.
- Hybrid Microsoft Entra Join: select this option if you want to join an existing AD DS environment. Once that’s done, the Cloud PC will be synchronized with Microsoft Entra.
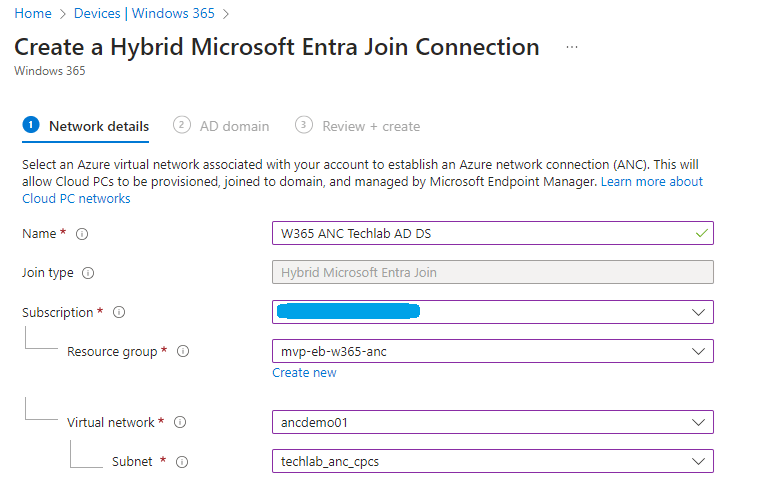
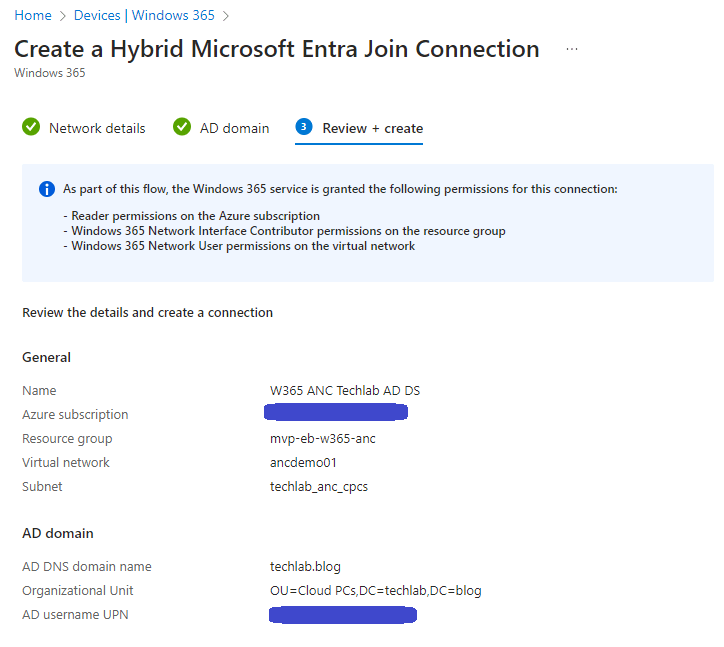
Let’s select Hybrid Microsoft Entra Join since we want to create a hybrid identity. Here are the steps we need to take to create the Azure Network connection. We will start by completing the Network details step:
- Name: provide a name for the ANC.
- Join type: Already filled in and greyed out.
- Subscription: select the subscription that has all the required resources.
- Resource group: select the desired resource group.
- Virtual network: select the virtual network that has a subnet for the Cloud PCs.
- Subnet: select the subnet where you want the Cloud PCs to live.
I ended up with something like this:
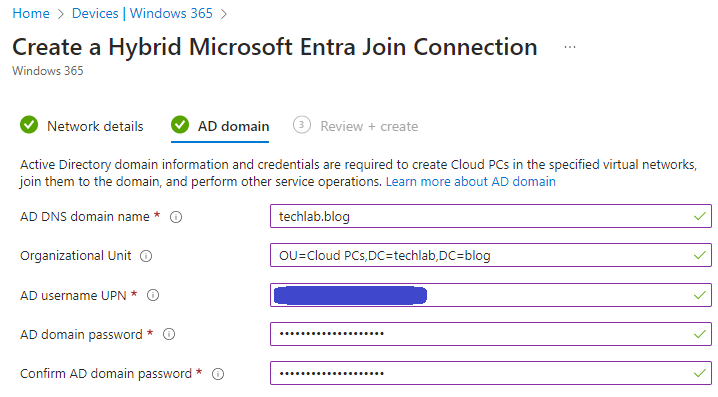
We can specify some domain properties in the second step named AD domain:
- AD DNS domain name: specify your AD DS domain
- Organizational Unit: this one is optional. You can specify the OU you want to use. (Example: OU=Cloud PCs,DC=techlab,DC=blog)
- AD username UPN: Specify the account that is used to join the Cloud PC to the domain.
- AD domain password: Specify the corresponding password.
- Confirm AD domain password: Same as above.
Admire your awesome work in the last step and create the ANC.
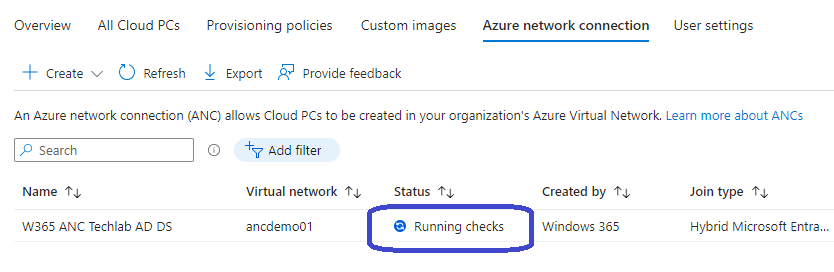
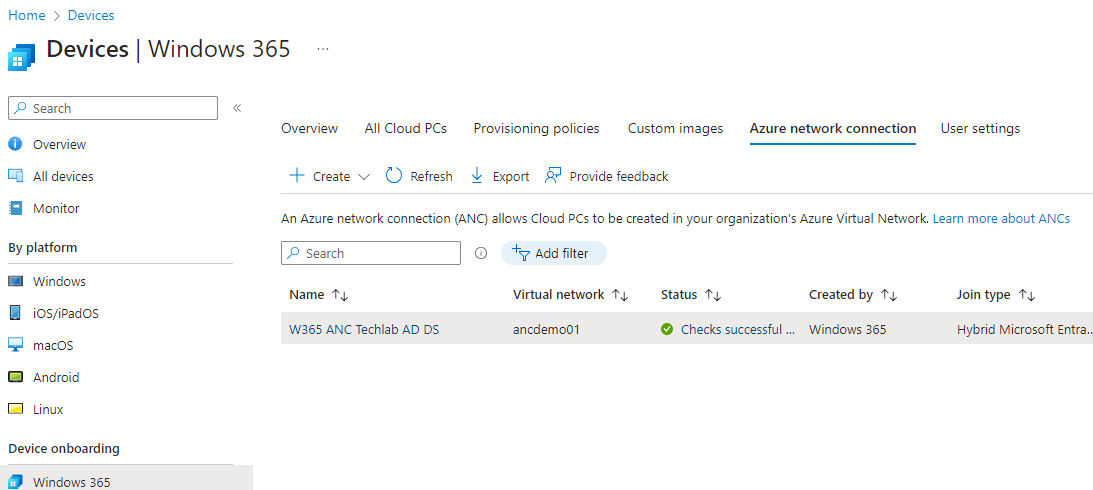
The newly created ANC will appear in the Azure network connection tab. The Windows 365 service will automatically run the checks to see if everything is configured correctly for the ANC.
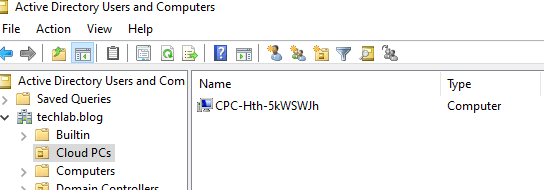
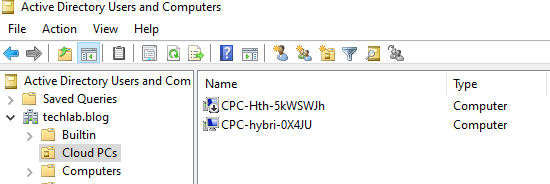
If you look closely at your AD, you might even see a (Cloud) PC object appear in the OU of your choice which is used for these checks:
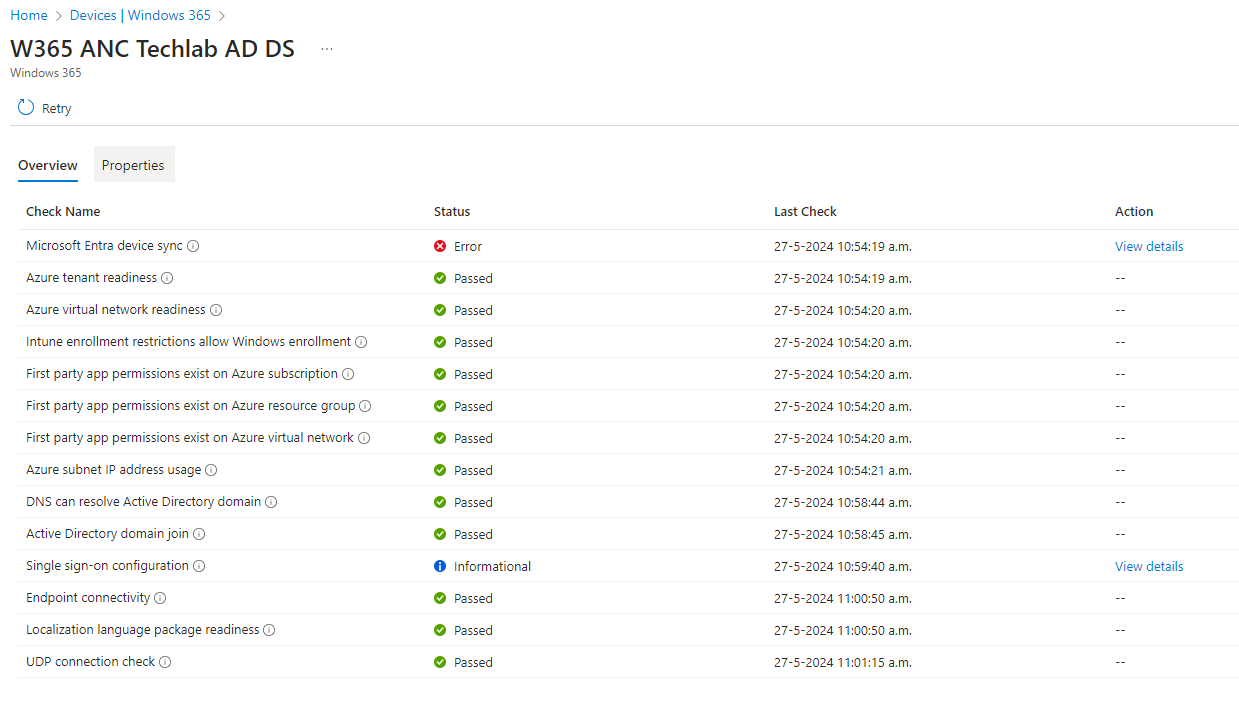
You can see which checks have been executed and their results if you click on the status.
In this demo I wanted to show if something went wrong, so I decided not to configure the device sync. That leads to this result:
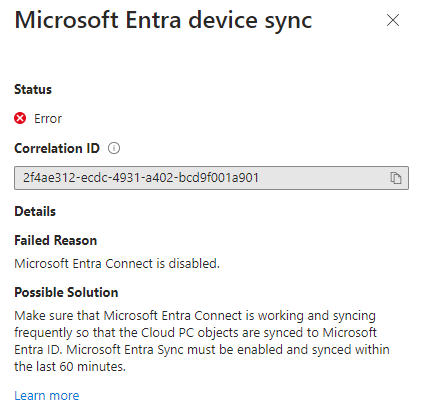
So what happens if a check fails? You will get a nice View details link next to it to get more information about the error and how to resolve the issue.
Since I have not configured the device sync, it will tell me to configure Microsoft Entra Connect to setup the device sync.
This needs to be solved before I can use this ANC in a provisioning policy, otherwise it will not appear in the dropdown box. I will not go into detail on how to do so in this post but you’ll need the status of checks successful.
Step 2: Deploying hybrid Cloud PCs
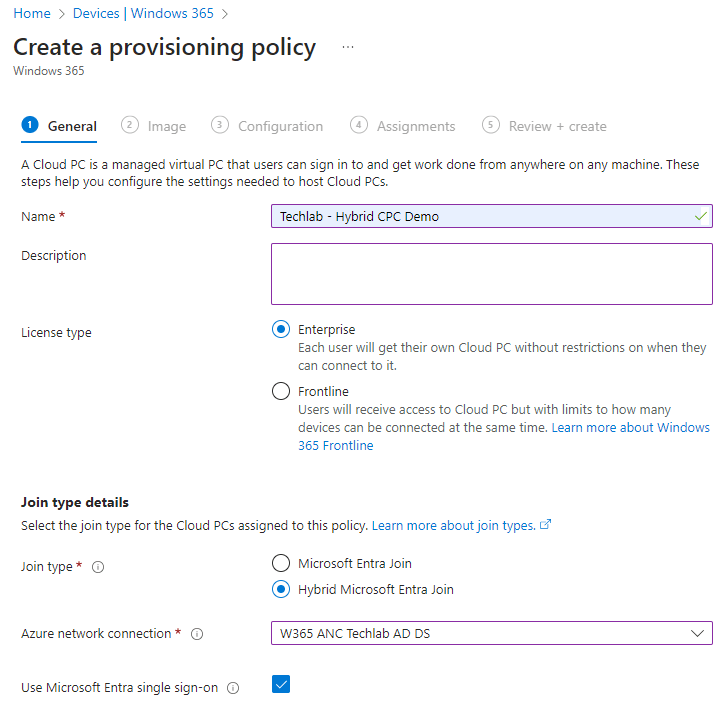
Deploying hybrid Cloud PCs is done using a provisioning policy. From the Microsoft Intune admin center, select Devices, Windows 365, Provisioning policies and select the + Create policy button in the ribbon.
Fill in the details as you normally would BUT make sure to select the Hybrid Microsoft Entra Join button. Then you can select the Azure network connection like this:
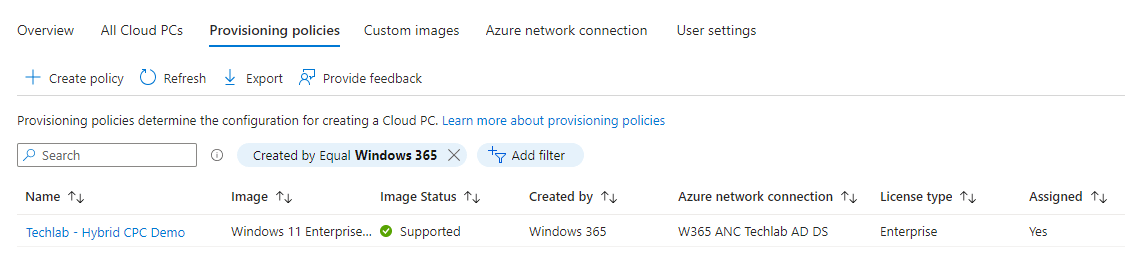
Continue like you normally would. Once finished you will see the newly created provisioning policy in the overview:
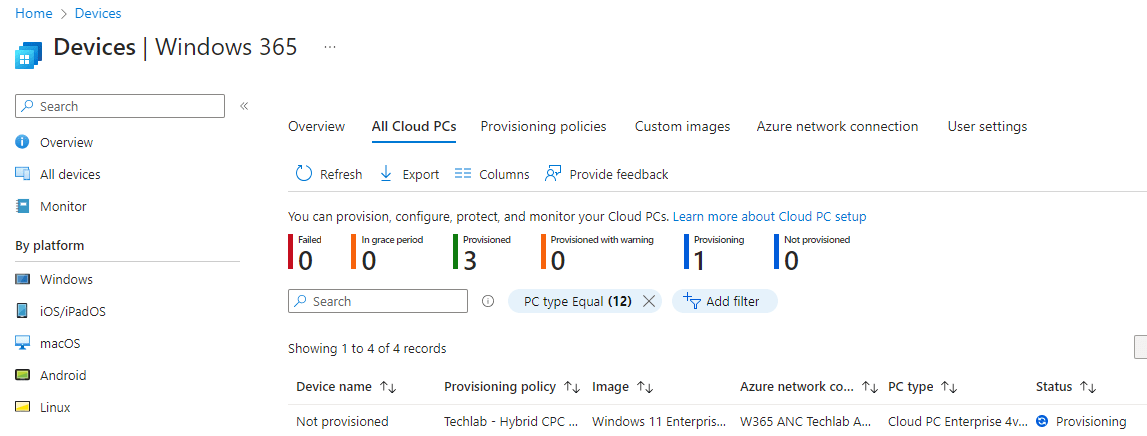
Next up, go to the All Cloud PCs tab and check if there’s a new Cloud PC deploying:
Now it’s time to let the Windows 365 service perform it’s magic and check back in once the Cloud PC is up and running.
Step 3: Manage hybrid Cloud PCs
Managing hybrid Cloud PCs can be done in a modern way using Microsoft Intune or a more traditional way, using Group Policies. Let’s use group policies in this demo to enable watermarking. Keep in mind that you will need to download the latest administrative templates for AVD (link) to configure this setting.
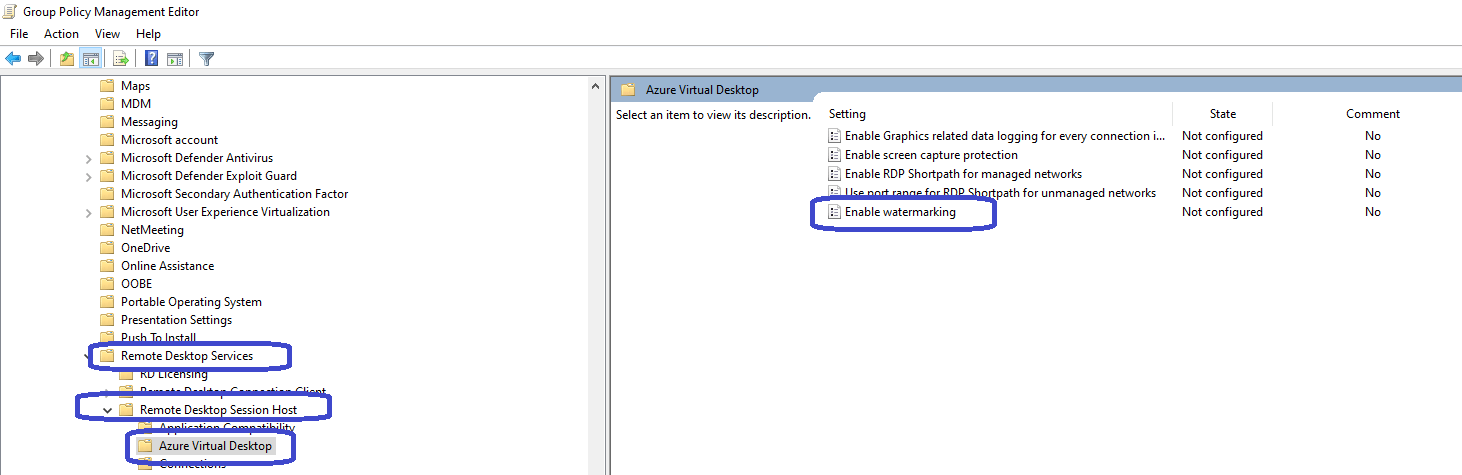
Create a new GPO and navigate to Computer Configuration, Administrative Templates, Windows Components, Remote Desktop Services, Remote Desktop Session Host, Azure Virtual Desktop and search for Enable watermarking.
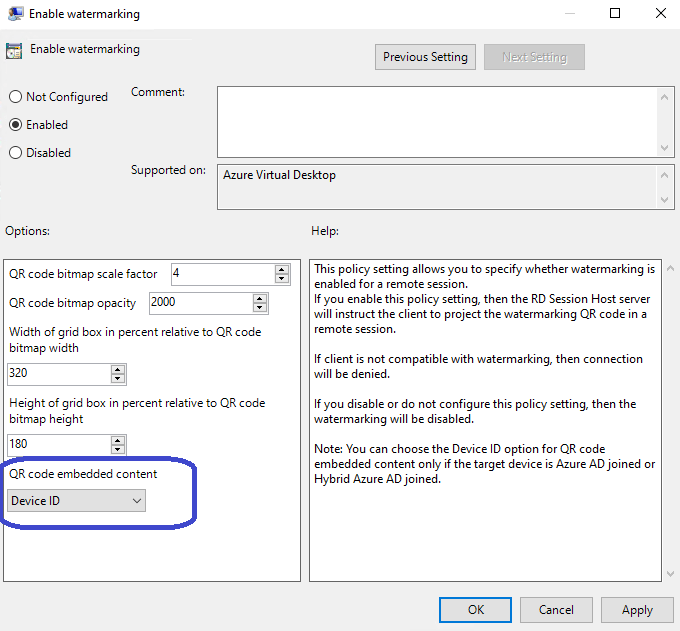
Configure the watermark to your liking BUT make sure to select Device ID as the QR code embedded content.
Why? You can’t do anything with a session ID on Windows 365, it’s meant for AVD. Instead use the Device ID. That can be tracked to a particular Cloud PC and since Cloud PCs are personal, it can be tracked to a user.
All that’s left do is to save the GPO and test it by signing into the Cloud PC and see if there’s a QR watermark present:
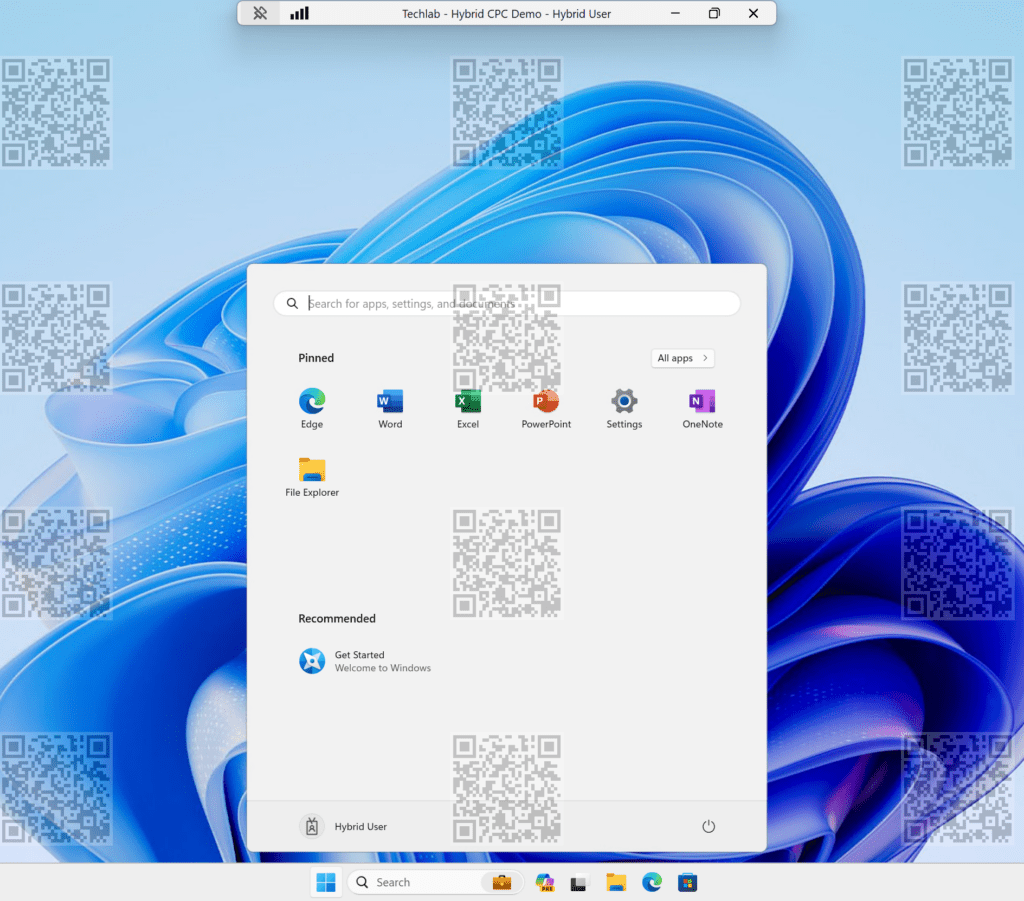
There you go! This Cloud PC is hybrid joined and managed via a group policy. The great thing about this is that you can mix-and-match meaning that you can also deploy Microsoft Entra joined Cloud PCs as well. It’s all part of the provisioning process magic.
Going off topic...
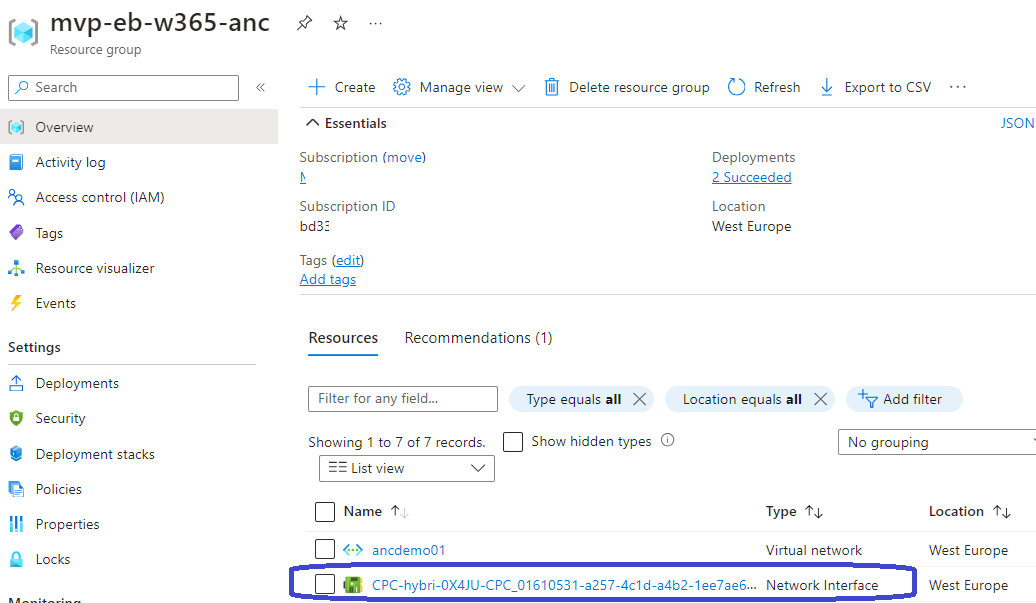
As usual, you cannot see the Cloud PC in the Azure portal. But in this scenario you can actually see the network interface in the Azure portal. All you need to do is to navigate to the resource group and you will find it there:
I would not recommend to fiddle around with the network interface but I do think it’s great to see that all the things needed fall into place behind the scenes! If you do fiddle around with this and you break your Cloud PC, don’t blame me! 🙂
Resources
I used the following resources for this post: